History of SSL/TLS
SSL (Secure Sockets Layer) and TLS (Transport Layer Security) are cryptographic protocols used to secure communication over the internet. They are similar but distinct security protocols and are often collectively referred to as “SSL/TLS.”
1.SSL (Secure Sockets Layer):
- SSL was initially developed by Netscape Communications Corporation in 1994.
- Its first version, SSL 1.0, was never publicly released due to numerous security vulnerabilities.
- SSL 2.0 emerged in 1995 and saw more widespread use, but its lifespan was short-lived due to security vulnerabilities.
- SSL 3.0, introduced in 1996, was more secure. However, over time, various security vulnerabilities were discovered, leading to the abandonment of SSL 3.0.
2.TLS (Transport Layer Security):
- TLS is considered an enhanced and secure version of SSL.
- TLS 1.0, introduced in 1999, is an improved version of SSL 3.0 with security vulnerabilities addressed.
- TLS 1.1 arrived in 2006, and TLS 1.2 followed in 2008, both enhancing the protocol’s security.
- TLS 1.3 was released in 2018, introducing numerous security and performance improvements. TLS 1.3 is faster and more secure compared to its predecessors.
SSL and TLS secure internet communication by encrypting traffic, ensuring the confidentiality of data exchanges, and updating security protocols. However, as vulnerabilities and weaknesses emerge, these protocols are continually updated and improved.
TLS 1.2 or TLS 1.3?
As of 2021, TLS 1.0 and TLS 1.1 have been officially deprecated.
Source
TLS 1.2:
- It is an older version and is supported by many applications and systems.
- It is a good option for establishing a secure connection but may have some security vulnerabilities.
- Security experts recommend using TLS 1.3 whenever possible instead of TLS 1.2.
TLS 1.3:
- It is a more recent version and offers a range of security improvements.
- It includes faster connection establishment times and more secure encryption algorithms.
- Designed to address security vulnerabilities, it is supported by many modern browsers and servers.
The version you should use depends on the systems, applications, and requirements in use. However, generally, you might prefer TLS 1.3 if possible, as it is more secure and offers better performance. Nevertheless, compatibility issues with older systems or specific requirements may necessitate the use of TLS 1.2.
Web servers and browsers typically automatically use up-to-date and supported TLS versions. If you manage a web server, it is advisable to use the latest and supported TLS version. As users, keeping your browsers and systems up-to-date is essential for enhancing security and ensuring optimal performance.
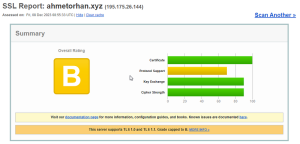
In this article, we will explore how to address the general SSL/TLS warnings provided by https://www.ssllabs.com/ssltest, a platform used to check and score the SSL/TLS security levels of the web hosting platforms. Additionally, we will conduct these checks on the test website https://ahmetorhan.xyz for demonstration purposes. The article will simplify the steps to disable the RC4 protocol and TLS 1.0 and TLS 1.1, especially focusing on how to implement these measures on Windows Servers. As indicated in the output, we will observe the necessity of disabling these protocols for enhanced security.
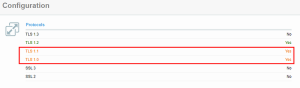
- Our objective here is to disable the deprecated TLS 1.0 and TLS 1.1, as indicated in the following sections.
SSL Security Registry Configuration
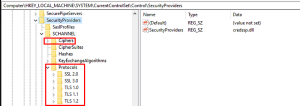
- Paste the provided code into a text document named “security_enable.txt.” Rename the file to “security_enable.reg” and remove the “.txt” extension.
Windows Registry Editor Version 5.00
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client]
"Enabled"=dword:00000001
"DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server]
"Enabled"=dword:00000001
"DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Client]
"Enabled"=dword:00000000
"DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1\Server]
"Enabled"=dword:00000000
"DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Client]
"Enabled"=dword:00000000
"DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0\Server]
"Enabled"=dword:00000000
"DisabledByDefault"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Client]
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 2.0\Server]
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Client]
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0\Server]
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\KeyExchangeAlgorithms\Diffie-Hellman]
"ServerMinKeyBitLength"=dword:00000800
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC4 128/128]
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC4 40/128]
"Enabled"=dword:00000000
[HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC4 56/128]
"Enabled"=dword:00000000- When we run the “security_enable.reg” file, all the entries above will be automatically added to the registry, and you can verify that they have been added as shown below.
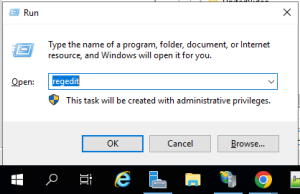
- Open regedit by following the path Start -> Run.
- After completing these steps, you need to restart your server for the changes to take effect.
- After the restart process is complete, I am initiating the test procedure again for the domain https://ahmetorhan.xyz. Initially classified as B, we now observe that it is categorized as A.
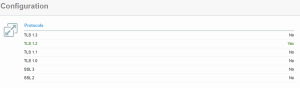
- You can observe that the TLS 1.0 and TLS 1.1 protocols have been disabled.
- If you want to revert the changes made in the registry, running the following entries and restarting will be sufficient.
Windows Registry Editor Version 5.00
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2]
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.1]
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.0]
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\SSL 3.0]
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\KeyExchangeAlgorithms\Diffie-Hellman]
"ServerMinKeyBitLength"=dword:00000800
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC4 128/128]
"Enabled"=dword:00000000
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC4 40/128]
"Enabled"=dword:00000000
[-HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Ciphers\RC4 56/128]
"Enabled"=dword:00000000If you have any questions or details you would like to add, feel free to write me.